Tech Against Terrorism
Did you ever wonder how your internet websites and applications manage terrorist activities? Do these applications and websites really help terrorist cells thrive and extend their web of influence? What are they doing to stop the terrorists?
After a previous conference I attended and blogged about, The International Tourism Security Summit in Jerusalem, was about the front end marketing and crisis management, I wanted to see how the back end handles it.
The Tech Against Terrorism group works with the GIFCT (Global Internet Forum to Counter Terrorism) which launched in 2017 by Twitter, Microsoft, Google and Facebook. GIFCT is trying to police the Internet and their own applications through the sharing of databases, resources and best practices. This is not a simple task considering the billions of transactions (postings, messages, attachments, etc.) happening daily.
The conference split into two parts, the morning sessions, which I attended, were about the efforts being made and also provided insights to changes in the way terrorists are working on the internet. After lunch was dedicated to the tech startups and businesses that wanted to do more, learn more, or be a part of the effort to fight terrorism.
We started out by hearing from Facebook’s Dr. Erin Saltman who is Policy Manager for EMEA and part of the Facebook Counter Terrorism team. She explained how Facebook maintains a huge staff, and is hiring more people, to manage the activities that not only get reported by every day users(hate speech, indecent pictures, etc.) but are flagged as questionable postings or pictures by their AI systems. Their AI system is not perfect, they know this, but it does get better every day. Postings that the AI can not easily classify are sent to a human for review.
This of course brought up a side discussion I had with Dr. Saltman about why somethings are rejected, and others are not, or why someone is banned, or not. While you may think, and feel, an item in question should be blocked, given how many items a Facebook employee reviews and in comparison to a prior case, mistakes can happen. Usually if you are reasonable and appeal your case they will listen to you. It was also interesting that the Facebook teams handling all of this are in specific locations and cover numerous languages so patterns that emerge can be acted on with better agility.
 Minister of Justice, Ayelet Shaked gave a brief talk about the things the Knesset is looking at and how Israel takes cyber warfare just as serious as physical warfare.
Minister of Justice, Ayelet Shaked gave a brief talk about the things the Knesset is looking at and how Israel takes cyber warfare just as serious as physical warfare.
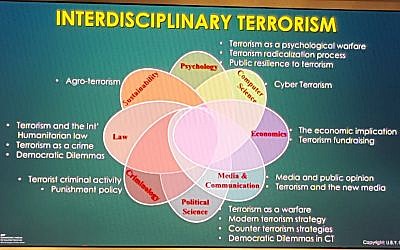
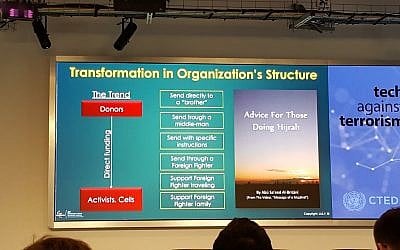
One of the more intriguing sessions was given by Uri Ben Yaakov from the International Institute for Counter Terrorism at IDC Herziliya. In his session he showed the various ways terrorist cells recruit, seek donations, push out their messages and how they take advantage of guerrilla marketing tactics. It would seem the terrorists learn from us and other non profits how to go about campaigning, donating and providing constituents with perks. Scarily it resembles the process of making aliyah or donating money to Friends of the IDF.
In short, it is a slow win scenario, as fast as we plug a hole, they find a new one. It is no longer enough to be vigilant in real life, we need to be vigilant online as well.
Report abuse, incitement, hate speech, graphical content that is disturbing and so many other things but keep in mind also each country is different. The “Freedom of Speech” the US grants people is not worldwide and while you, as an American, living outside of the US, may not like what people say or post, there may not be any law against it, in their part of the world. This is where Facebook and the other applications have to come together to police the internet, yet stay within the legal boundaries.
Interestingly, What’s App which has secure point to point communications presents Facebook with problems about how to invade privacy, if possible, to prevent the app from being used nefariously. Security works in our favor, but also the terrorists in this case.
If you are a startup that manages communications, calendars, payments, chat groups and numerous other aspects of social interactions, you probably should look deeper into what your customers are doing with your app.The GIFCT is available for more discussions and encourages companies to reach out via their website, gifct.org or email them at outreach@gifct.org.





